C-Rex Suite Features
C-Rex Fangs
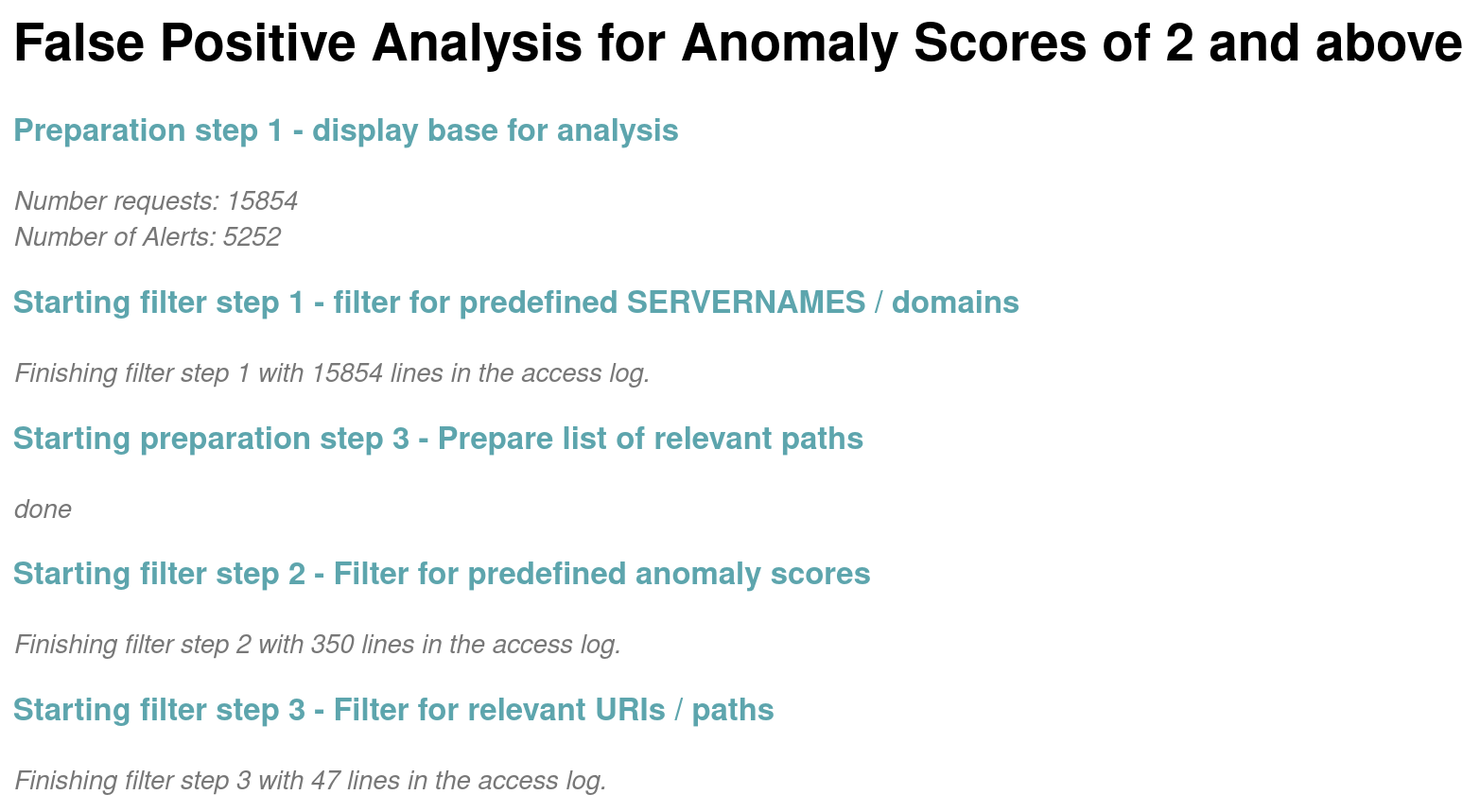
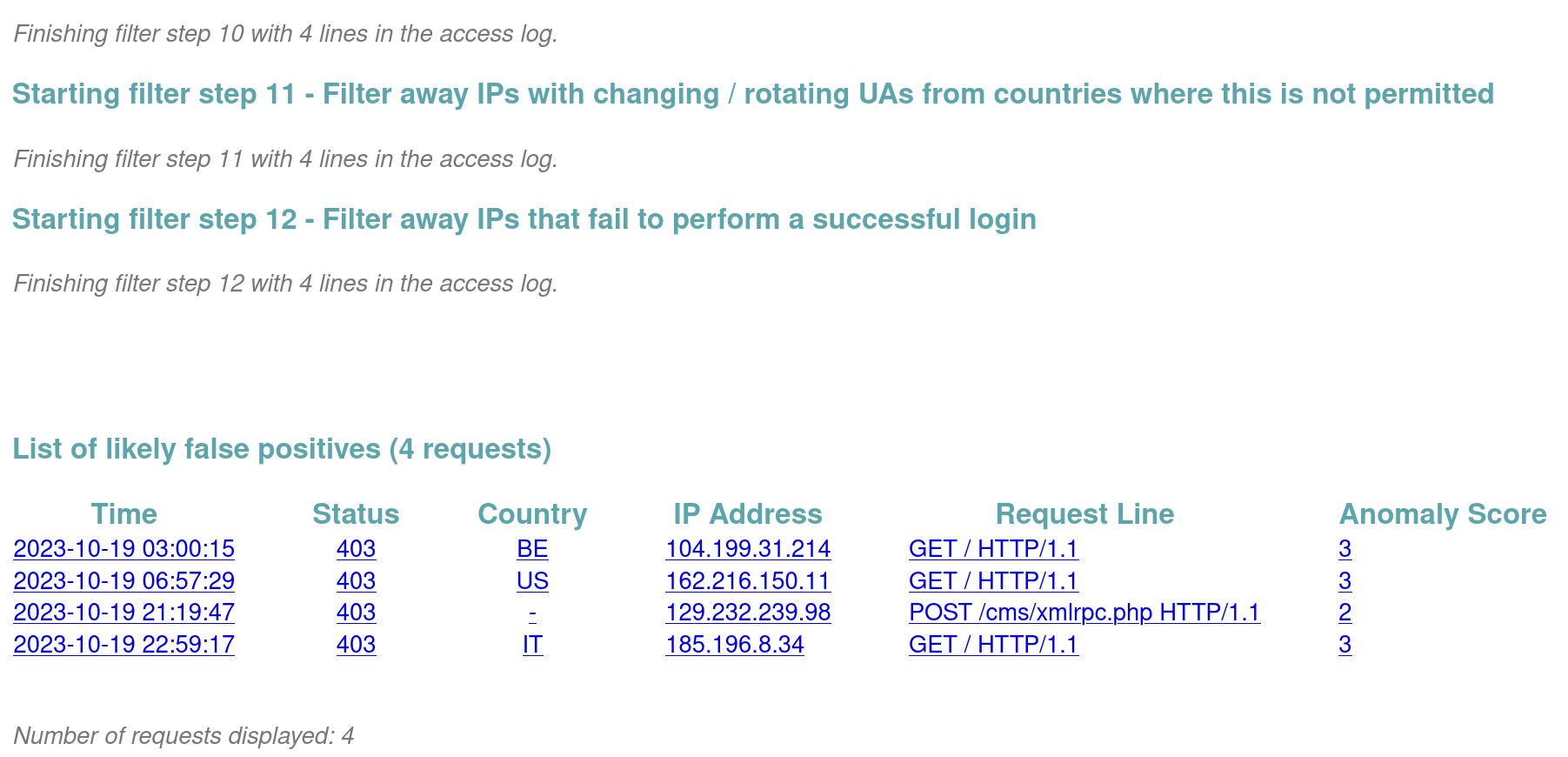
C-Rex Fangs singles out false positives in large haystacks through an elaborate filtering process.
C-Rex Arms
C-Rex Arms guides the user to address individual false positives via an intuitive wizard style GUI.
Rule Exclusions
C-Rex supports all four classic rule exclusion methods with a single click.
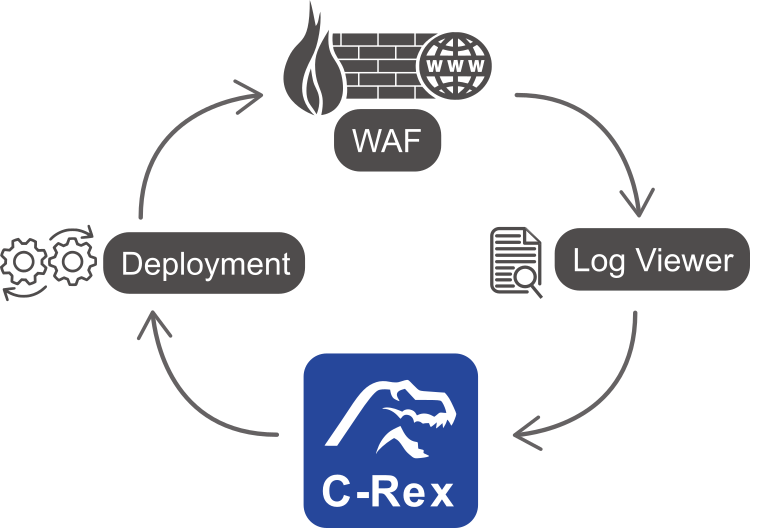
Integration
C-Rex integrates easily with existing log viewer and CI/CD setups.
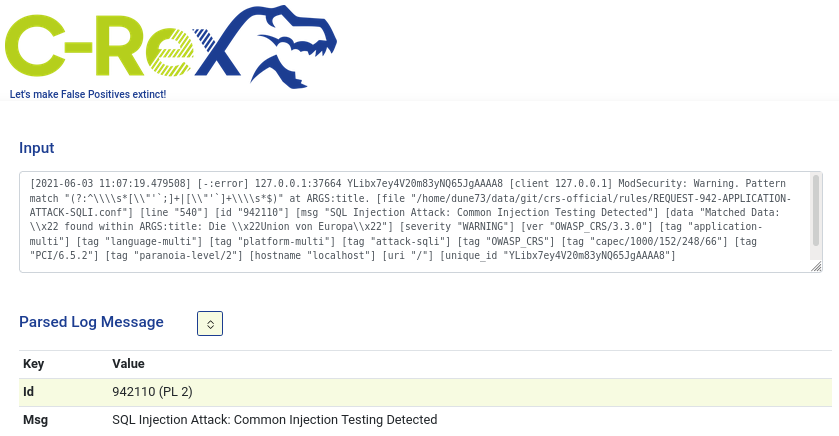
Parsing
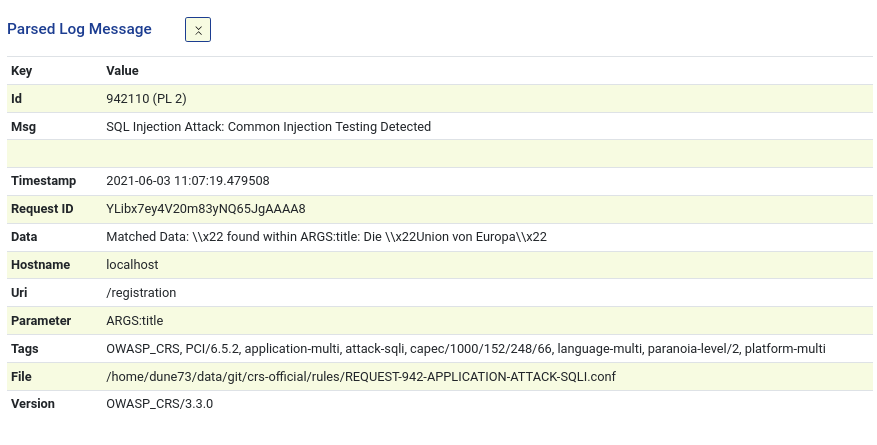
C-Rex parses the full variety of all ModSecurity alert messages across multiple versions.
CRS Integration
Created by CRS Co-Lead Christian Folini; C-Rex knows CRS by heart and it knows how to address all special cases.
C-Rex Fangs identifies the False Positives for you
A service exposed on the internet is constantly under attack. The WAF will produce a huge amount of alerts every day. Interleaved with the attacks might be false positives where the WAF mis-identified your legitimate users as attackers. You need to handle these false positives to unblock your users. But singling out the alerts is like searching needles in a haystack. C-Rex Fangs applies series of filters to the alerts in order to minimize the size of the haystack. By default, this reduces the triage volume by over 90%, often 99%.
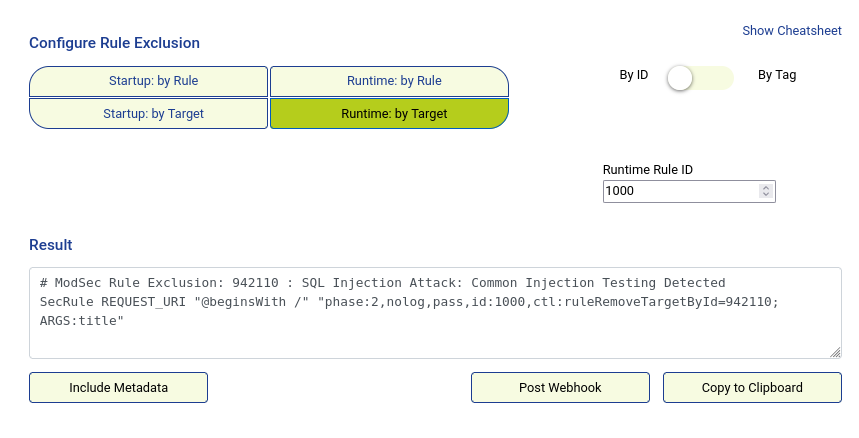
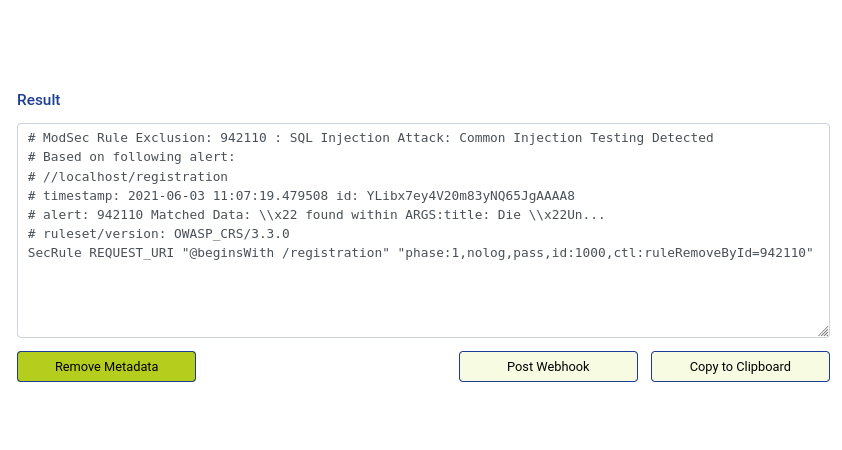
C-Rex Arms writes the Rule Exclusions for you
A rule exclusion instructs the WAF to skip a rule in an individual context and C-Rex Arms is your assistant when writing these rule exclusions. There are four canonical types of ModSecurity rule exclusions and two of them are really hard to write by hand. C-Rex Arms supports this crucial step: It helps you create a rule exclusion that you can tweak to your needs with a wizard style graphical interface.
Your data, your premises
In a minimal setup, you copy the alert message into the GUI, let C-Rex do its thing and then you paste the output back into your WAF configuration. Everything runs in a container on your server. No cloud, no phone-home, not even an internet connection is required.
Full integration
In a more advanced setup, you jump into C-Rex right from within your logviewer and you feed the rule exclusion into your CI/CD pipeline afterwards. This gives you a seamless integration of the WAF configuration and the CI/CD. It therefore enables your developers to tune away false positives without an extensive understanding of ModSecurity syntax and without asking the WAF or network security team for support. The C-Rex suite is the toolset that allows you to successfully integrate the WAF into your DevOps methodology.
From the CRS experts
netnea has been doing ModSecurity since 2005 and our Christian Folini wrote the 2nd edition of the ModSecurity Handbook. Meanwhile he has grown into one of the public faces of the OWASP Core Rule Set project (CRS). Most people use CRS when they speak of CRS and CRS also powers more than half of the commercial WAF market. C-Rex is a natural product of many, many years of practical ModSecurity use.

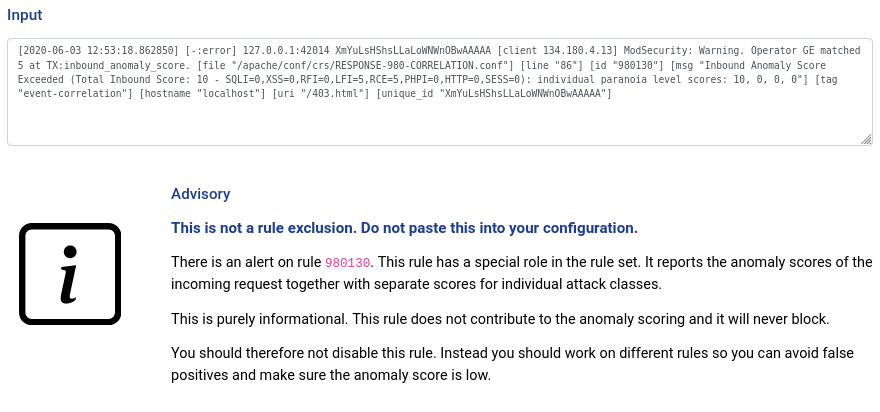
C-Rex knows the nitty gritty details
C-Rex knows CRS by heart. This is important since writing CRS rule exclusions can lead to a total WAF bypass when you disable the wrong rule by accident (rule id 949110!). But with the C-Rex suite by your side, there is nothing to worry about: C-Rex will warn you when you get too close to the quicksand. Instead, it will tell you how to deal with the situation appropriately.